A barcode is a machine-readable code that comes in the form of numbers and patterns of parallel lines of different widths, and is often used to store retail product information. There are handheld barcode readers, which are generally used in warehouses and department stores, to scan various product information, such as details such as prices….
In the automotive industry, there is a lot of talk about electric vehicles. Green is the trend right now. While the demand for electric vehicles has been on the rise, there is a limited supply of new and used electric vehicles. A popular option is to convert a car to an electric one. Many engineers and…
In the previous article, we talked about bash functions and how to use them directly from the command line, and we also saw some other cool stuff. Today we’re going to talk about a handy string manipulation tool called sed or sed Linux commands. We use SEDs to process text files such as log files, configuration…
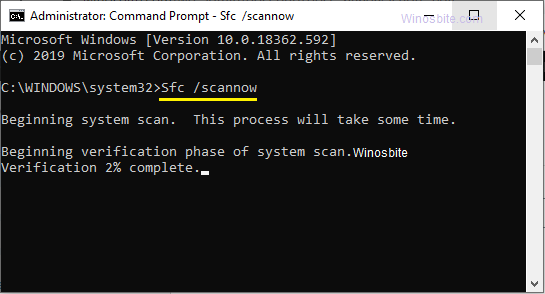
This is a common Windows 10 update error code 0x80070490 that doesn’t allow you to install any of the latest updates. In short, 0x80070490 is an error code that indicates that there is any problem with the Windows Update operation. This issue occurs because the files related to component-based services and system component storage are…
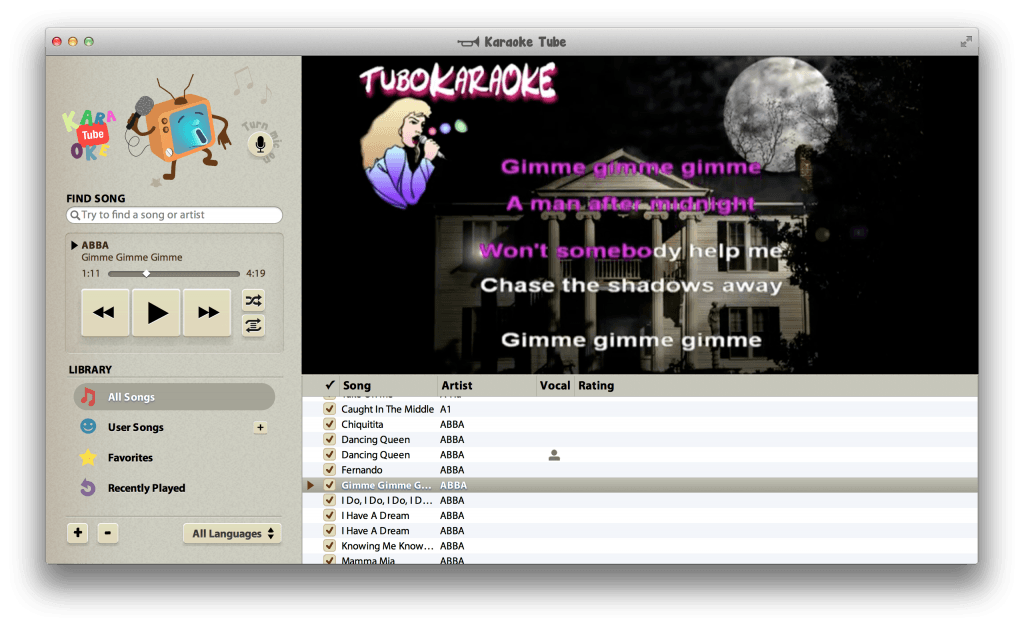
Karaoke software on Mac is not as common as it is on PC, but here we have looked at the best karaoke software for Mac users. What are the best karaoke software? Whether you’re just looking to spice up the party with some impromptu drunken karaoke or you’re looking for professional karaoke software, with this…
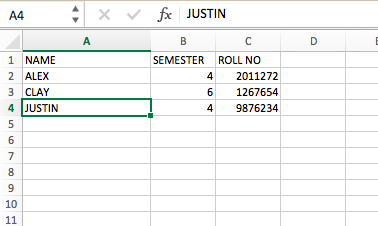
Using the XLRD module, information can be retrieved from spreadsheets. For example, you can read, write, or modify data in Python. In addition, users may have to go through various worksheets and retrieve data based on certain criteria or modify certain rows and columns and do a lot of work. The RD module is used…
When you try to transfer or access any data from an external hard drive connected to your computer, you may face a situation where you cannot access the drive. The parameter is incorrect, wrong. This happens when your external hard drives, USB devices, SD cards, and other devices are accidentally attacked. If you have any issues…
As the word suggests, hacking has nothing to do with any morality. Hacking is the attempt to force access to someone’s system with a fraudulent mindset in order to compromise his privacy or steal his system data. Still, if weaknesses and threats to a computer network or individual unit are identified with implicit and approved…
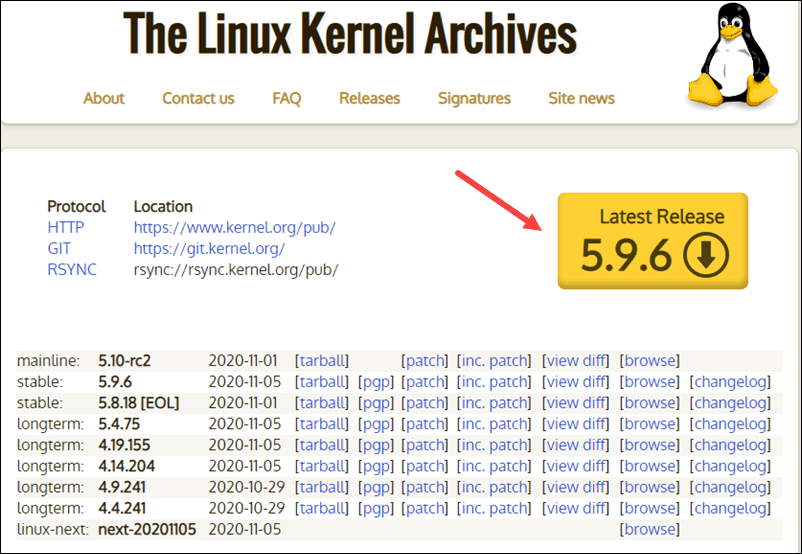
Introduction to the Linux kernel construction tutorial The Linux kernel is the foundation of a Unix-like operating system. The kernel is responsible for the communication between hardware and software and the allocation of available resources. All Linux distributions are based on a predefined kernel. However, if you want to disable multiple options and drivers or…
Keeping your car in accessory mode may be just what you need while you wait. Some people want to use it for hours on end while waiting for a friend or stalking an ex-girlfriend (please don’t do it). Therefore, it is a common question to wonder how long the battery will last in accessory mode….